The Onion Router which is most commonly known as Tor, is a wonderful tool for anonymizing your online activity. Tor consists of public proxies setup by trusted members of the Tor community, who allow other users to make use of their proxies to browse the web. In a typical Tor session, there are at least 3 proxies involved, making it very difficult to trace back any online activity to a single user. Furthermore, the communication between the client and the proxies are tunnelled in layers, providing protection against casual snooping as well.
Setting up Tor on Linux was surprisingly easy. Tor binaries are available in the Fedora repositories, so just simply type
sudo yum install tor
Once installed, invoke Tor by typing
tor
The Tor client will start up and attempt to establish a proxy chain. Once this is complete, it will start a SOCKS proxy on port 9050. To Torrify any application, you simply have to configure it to use the proxy server created by Tor at 127.0.0.1:9050.
If you want to completely anonymize your browsing, there's an additional step involved. Usually applications such as web browsers do not use the SOCKS proxy to tunnel DNS queries. This can lead to information leakage because anyone listening in can see by the DNS query that you're attempting to visit that certain site. Therefore even if your data is secure, your browsing history is not.
The simplest solution is to use a HTTP proxy such as Privoxy and configure it to use Tor. This way you can achieve quite a good level of anonymity online without any hassle.
Privoxy is also available in the repositories, so installation is a breeze.
sudo yum install privoxy
Afterwards, you need to configure it to forward requests through Tor.
sudo echo "forward-socks4a / 127.0.0.1:9050 ." >> /etc/privoxy/config
Start the Privoxy daemon by typing
sudo privoxy /etc/privoxy/config
Configure your browser to use an HTTP proxy at 127.0.0.1:8118 and restart it. If everything went smoothly, you're now browsing anonymously. The best way to see this in action is to open up www.google.com. Depending on the location of the Tor exit node, you will be served with a Google page for that specific region. For example, when I tried it, I was served the Google Denmark page because my Tor exit node was in Denmark. You can also use tools like http://whatismyipaddress.com/ to see how your IP has changed completely due to Tor.
The internet is a wild place. If you are worried about privacy, give Tor a spin. It's definitely a good tool to have handy.
Friday, 26 September 2008
Thursday, 25 September 2008
Thursday, 18 September 2008
CrossOver Chromium - Run Chrome on Linux and Mac
Google's Chrome browser (http://www.google.com/chrome) got a lot of attention when it was initially released, and deservingly so. I personally like most of the features implemented in Chrome, but unfortunately the lack of a Linux port makes it harder to test it out. I tried running Chrome with Wine, but there were few configurations that needed to be done that I didn't have time for. Therefore, my Chrome experiments had to be shelved for a later time.
Now thanks to Codeweavers, the company behind the CrossOver Office product, the open source version of Chrome is available as CrossOver Chromium (http://www.codeweavers.com/services/ports/chromium/) for both Linux and Mac users to try out using Wine. This is a wonderful effort by Codeweavers that goes to show how mature Wine has become and how easily adaptable it is.
Installing CrossOver Chromium is a breeze. Just grab the setup from the Codeweavers website and run it. The installer will automatically take care of the rest.
wget http://media.codeweavers.com/pub/crossover/chromium/install-cxchromium-0.9.0.sh
sh install-cxchromium-0.9.0.sh
CrossOver Chromium is quite stable and responsive in my Fedora 9 box. Ofcourse, HTTPS connections will not work because the libraries are not yet fully implemented on Wine. Although Flash is installed using winetricks, Crossover Chromium doesn't seem to recognize it. So Flash animations are out of order at the moment as well.
As clearly mentioned in the Codeweavers site, CrossOver Chromium is not intended as a full software distribution. It is just a proof-of-concept that any sufficiently complex Windows program can be ported to Wine with minimal effort. I think Codeweavers have managed to prove this point splendidly and in the process have enabled us Linux users to experience Chrome without having to boot Windows. Kudos to the team at Codeweavers for the effort.



Now thanks to Codeweavers, the company behind the CrossOver Office product, the open source version of Chrome is available as CrossOver Chromium (http://www.codeweavers.com/services/ports/chromium/) for both Linux and Mac users to try out using Wine. This is a wonderful effort by Codeweavers that goes to show how mature Wine has become and how easily adaptable it is.
Installing CrossOver Chromium is a breeze. Just grab the setup from the Codeweavers website and run it. The installer will automatically take care of the rest.
wget http://media.codeweavers.com/pub/crossover/chromium/install-cxchromium-0.9.0.sh
sh install-cxchromium-0.9.0.sh
CrossOver Chromium is quite stable and responsive in my Fedora 9 box. Ofcourse, HTTPS connections will not work because the libraries are not yet fully implemented on Wine. Although Flash is installed using winetricks, Crossover Chromium doesn't seem to recognize it. So Flash animations are out of order at the moment as well.
As clearly mentioned in the Codeweavers site, CrossOver Chromium is not intended as a full software distribution. It is just a proof-of-concept that any sufficiently complex Windows program can be ported to Wine with minimal effort. I think Codeweavers have managed to prove this point splendidly and in the process have enabled us Linux users to experience Chrome without having to boot Windows. Kudos to the team at Codeweavers for the effort.



Thursday, 11 September 2008
Spice up the command line with BashStyle-NG
What I like most about Linux is its powerful command line. Many people find it intimidating, but with a little practice, the command line is the most natural way of interacting with a computer. Things can be done with the command line in less time than it takes to just launch the equivalent GUI utility.
The term "command line" naturally doesn't invoke a very pleasant image because we have come to associate it with a bland, colourless screen filled with text. But in reality, things can't be more further from the truth. X based terminal utilities allow a variety of customizations to tweak the appearance to fit the user's needs. It's well worth the effort to spend some time tweaking the terminal to fit your taste, because sooner or later, you are sure to come across a task that is more easily accomplished using the command line than the GUI.
BashStyle-NG (http://freshmeat.net/projects/bsng/?branch_id=75809&release_id=284647) is a GUI utility that allows the user to customize the command line in more innovative ways. Some of the options provided include:
Installing BashStyle-NG is quite easy. Grab the source tarball from http://freshmeat.net/redir/bsng/75809/url_bz2/BashStyle-7.1.tar.bz2 and configure, make and make install !
BashStyle uses the python-psyco compiler to speed up execution times. It's a good idea to install it before beginning the actual installation.
sudo yum install python-psyco
wget http://freshmeat.net/redir/bsng/75809/url_bz2/BashStyle-7.1.tar.bz2
tar xvf BashStyle-7.1.tar.bz2
cd bashstyle
./configure
make && sudo make install
On my machine, BashStyle-NG got installed with root as the owner. This prevented some of the customizations from working correctly when run as a normal user. To fix this, change the permissions of the BashStyle-NG script.
sudo chmod 0777 /usr/share/bashstyle-ng/system/nx-rc
Now all that's left is to invoke BashStyle and start customizing !
bashstyle


The term "command line" naturally doesn't invoke a very pleasant image because we have come to associate it with a bland, colourless screen filled with text. But in reality, things can't be more further from the truth. X based terminal utilities allow a variety of customizations to tweak the appearance to fit the user's needs. It's well worth the effort to spend some time tweaking the terminal to fit your taste, because sooner or later, you are sure to come across a task that is more easily accomplished using the command line than the GUI.
BashStyle-NG (http://freshmeat.net/projects/bsng/?branch_id=75809&release_id=284647) is a GUI utility that allows the user to customize the command line in more innovative ways. Some of the options provided include:
- The ability to tweak the prompt in interesting ways to display important information in various colours.
- Colourizing output from tools like grep and man for easy readability
- Creating aliases
- Tweak command history, auto completion and internal variables such as the default editor
- Change behaviour of editors such as vim and nano
- Manage user profiles
Installing BashStyle-NG is quite easy. Grab the source tarball from http://freshmeat.net/redir/bsng/75809/url_bz2/BashStyle-7.1.tar.bz2 and configure, make and make install !
BashStyle uses the python-psyco compiler to speed up execution times. It's a good idea to install it before beginning the actual installation.
sudo yum install python-psyco
wget http://freshmeat.net/redir/bsng/75809/url_bz2/BashStyle-7.1.tar.bz2
tar xvf BashStyle-7.1.tar.bz2
cd bashstyle
./configure
make && sudo make install
On my machine, BashStyle-NG got installed with root as the owner. This prevented some of the customizations from working correctly when run as a normal user. To fix this, change the permissions of the BashStyle-NG script.
sudo chmod 0777 /usr/share/bashstyle-ng/system/nx-rc
Now all that's left is to invoke BashStyle and start customizing !
bashstyle


Thursday, 24 July 2008
Encrypted removable storage with Fedora 9
Linux Unified Key Setup (LUKS) is a way to create encrypted disk partitions on Linux. It has been around for a while now, and Fedora 9 provides LUKS support out of the box. Encrypted partitions can be configured to be unlocked with several passphrases, allowing many users to share the partition. Disk access speeds are almost comparable to that of unencrypted disks. Best of all, LUKS is cross-platform. Even Windows users are able to use an encrypted partition created with LUKS.
The number of material on the net about creating LUKS partitions is surprisingly low. The few link I checked out only detailed how to setup permanent encrypted partitions that got mounted at every bootup. My requirement was to encrypt an external hard-drive that I use for backup purposes, therefore I set out to find out the process of encrypting a removable disk on my own. I was helped along the way by http://fedoraproject.org/wiki/Security_Guide/9/LUKSDiskEncryption and http://www.saout.de/tikiwiki/tiki-index.php?page=EncryptedDeviceUsingLUKS
Step 1:
Change in to the single user mode.
telinit 1
Step 2:
Check whether the drive is still mounted. (My drive is plugged in to /dev/sdb. Yours may vary)
mount | grep sdb
Unmount the drive if it is still mounted.
umount /dev/sdb
Step 3 (Optional):
For maximum security, the drive must be filled with random data. This can be done in two ways. Both methods are effective, but take a long time. You will possibly have to leave the process overnight to complete. Be warned; this step will OVERWRITE ALL DATA on the disk.
Method 1:
Use dd to write data from /dev/urandom. Make sure you type it correctly. If you type /dev/random by mistake, your grand-kids will be wrinkled and toothless by the time it finishes.
dd if=/dev/urandom of=/dev/sdb
Method 2:
Suggested by LUKS wiki. Kills two birds with one stone by writing random data to the disk and checking it for errors at the same time.
badblocks -c 10240 -s -w -t random -v /dev/sdb
Step 4:
Create the LUKS partition.
cryptsetup --verbose --verify-passphrase luksFormat /dev/sdb
Step 5:
Load the logical encrypted device.
cryptsetup luksOpen /dev/sdb my_enc_drive
This command will create /dev/mappers/my_enc_drive. You can provide any name you like in place of "my_enc_drive". To check whether the command succeeded, type:
ls -l /dev/mappers
You should see a new entry titled "my_enc_drive" in the output.
Step 6:
Create the file system. You can choose any file system you like. Be aware of permission problems when using secure file systems such as ext3. In this case, I am creating an ext3 file system on the encrypted disk.
mkfs.ext3 /dev/mapper/my_enc_drive
Step 7:
Mount the drive.
mount -t ext3 /dev/mapper/my_enc_drive /media/my_enc_drive
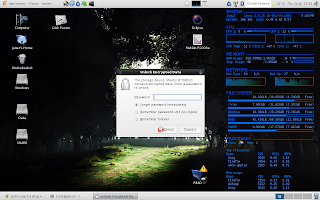
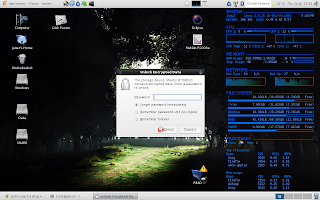
If everything went successfully, your encrypted file system is ready now. Reboot the computer to bring up the desktop and plug the drive in. It is automatically recognized as an encrypted drive and you will be prompted for a password.
In theory, the drive should be mounted automatically after you enter the password. But on my machine, the entry to /dev/mapper was automatically created, but the drive wasn't mounted automatically. I still haven't found the reason for this behaviour, but it is only a minor setback. The drive can be used without any problem by manually mounting it.
sudo mount -t ext3 /dev/mapper/luks_crypto_8e8d6392-7be3-4964-8e6d-9de57e886fa5 /media/my_enc_drive
" luks_crypto_8e8d6392-7be3-4964-8e6d-9de57e886fa5" is the name automatically generated by the HAL daemon. Yours will definitely be different.
To unmount the drive after using it. Simply type:
sudo umount /media/my_enc_drive
sudo cryptsetup luksClose luks_crypto_8e8d6392-7be3-4964-8e6d-9de57e886fa5
LUKS can be a viable alternative to TrueCrypt. The disk access speeds seem much better compared to TrueCrypt, at least on my machine. Best of all, LUKS comes pre-installed with Fedora 9. Therefore you don't need to struggle with getting the sources and compiling TrueCrypt.
The number of material on the net about creating LUKS partitions is surprisingly low. The few link I checked out only detailed how to setup permanent encrypted partitions that got mounted at every bootup. My requirement was to encrypt an external hard-drive that I use for backup purposes, therefore I set out to find out the process of encrypting a removable disk on my own. I was helped along the way by http://fedoraproject.org/wiki/Security_Guide/9/LUKSDiskEncryption and http://www.saout.de/tikiwiki/tiki-index.php?page=EncryptedDeviceUsingLUKS
Step 1:
Change in to the single user mode.
telinit 1
Step 2:
Check whether the drive is still mounted. (My drive is plugged in to /dev/sdb. Yours may vary)
mount | grep sdb
Unmount the drive if it is still mounted.
umount /dev/sdb
Step 3 (Optional):
For maximum security, the drive must be filled with random data. This can be done in two ways. Both methods are effective, but take a long time. You will possibly have to leave the process overnight to complete. Be warned; this step will OVERWRITE ALL DATA on the disk.
Method 1:
Use dd to write data from /dev/urandom. Make sure you type it correctly. If you type /dev/random by mistake, your grand-kids will be wrinkled and toothless by the time it finishes.
dd if=/dev/urandom of=/dev/sdb
Method 2:
Suggested by LUKS wiki. Kills two birds with one stone by writing random data to the disk and checking it for errors at the same time.
badblocks -c 10240 -s -w -t random -v /dev/sdb
Step 4:
Create the LUKS partition.
cryptsetup --verbose --verify-passphrase luksFormat /dev/sdb
Step 5:
Load the logical encrypted device.
cryptsetup luksOpen /dev/sdb my_enc_drive
This command will create /dev/mappers/my_enc_drive. You can provide any name you like in place of "my_enc_drive". To check whether the command succeeded, type:
ls -l /dev/mappers
You should see a new entry titled "my_enc_drive" in the output.
Step 6:
Create the file system. You can choose any file system you like. Be aware of permission problems when using secure file systems such as ext3. In this case, I am creating an ext3 file system on the encrypted disk.
mkfs.ext3 /dev/mapper/my_enc_drive
Step 7:
Mount the drive.
mount -t ext3 /dev/mapper/my_enc_drive /media/my_enc_drive
If everything went successfully, your encrypted file system is ready now. Reboot the computer to bring up the desktop and plug the drive in. It is automatically recognized as an encrypted drive and you will be prompted for a password.
In theory, the drive should be mounted automatically after you enter the password. But on my machine, the entry to /dev/mapper was automatically created, but the drive wasn't mounted automatically. I still haven't found the reason for this behaviour, but it is only a minor setback. The drive can be used without any problem by manually mounting it.
sudo mount -t ext3 /dev/mapper/luks_crypto_8e8d6392-7be3-4964-8e6d-9de57e886fa5 /media/my_enc_drive
" luks_crypto_8e8d6392-7be3-4964-8e6d-9de57e886fa5" is the name automatically generated by the HAL daemon. Yours will definitely be different.
To unmount the drive after using it. Simply type:
sudo umount /media/my_enc_drive
sudo cryptsetup luksClose luks_crypto_8e8d6392-7be3-4964-8e6d-9de57e886fa5
LUKS can be a viable alternative to TrueCrypt. The disk access speeds seem much better compared to TrueCrypt, at least on my machine. Best of all, LUKS comes pre-installed with Fedora 9. Therefore you don't need to struggle with getting the sources and compiling TrueCrypt.
Sunday, 13 July 2008
Secure File Deletion With srm
On any operating system, files deleted using the built-in file deletion utilities are never really deleted. Behind the scenes, deletion is simply a matter of removing the file from the directory entry and adding the blocks occupied by the file to the free block list. The file still exists on the disk like a ghost. The OS might reuse some of the blocks for another file, but it's not guaranteed that the whole file will get overwritten, therefore enough sensitive data from deleted files can be recovered with even the simplest of utilities. Even if all the blocks get casually overwritten, there are sophisticated methods that can be employed by a determined attacker to recover most of the overwritten data from a hard drive platter.
srm is a project that attempts to provide secure file deletion options to the familiar rm command used in all Unix derivatives. srm is fully compatible with the regular rm command, therefore there's no learning curve involved. There are 3 options for secure deletion.
Although it is dificult to guarantee total security, srm is a good open source solution for normal users who wish to keep their data private. A determined government agency might still get to your data, but certainly not your pesky script-kiddie cousin.
srm is a project that attempts to provide secure file deletion options to the familiar rm command used in all Unix derivatives. srm is fully compatible with the regular rm command, therefore there's no learning curve involved. There are 3 options for secure deletion.
- -s, --simple : Simple one pass overwriting with random data. (Least secure option.)
- -P, --openbsd : Emulates OpenBSD behaviour by overwriting in 3 passes.
- -D, --dod : Conforms to the US DoD specification of overwriting in 7 passes.
Although it is dificult to guarantee total security, srm is a good open source solution for normal users who wish to keep their data private. A determined government agency might still get to your data, but certainly not your pesky script-kiddie cousin.
Tuesday, 8 July 2008
WPA issues in Kernel 2.6.25.9-76
After accepting an auto update to the kernel which installed kernel 2.6.25.9-76, Fedora 9 failed to connect to WPA enabled wireless networks. The network manager applet kept attempting to connect and failing, repeatedly prompting for the WPA key without any success. Attempting to connect manually using the iwconfig commands also failed when attempting to obtain a DHCP lease using dhclient. Connecting to a WEP network succeeded, suggesting that the problem lay with WPA support. Restarting the wpa-supplicant service with service restart wpa_supplicant failed with the error Starting wpa_supplicant: /etc/wpa_supplicant/wpa_supplicant.conf, , dbus_bus_request_name[dbus]: Resource temporarily unavailable. At this point I was stymied with no possible solution coming to mind except reverting back to the old kernel, which worked perfectly. Judging by the bugzilla report, the problem appeared to be related to a couple of wireless fixes incorporated in to the kernel.
At this point, I decided to wait a couple of days for an updated kernel to be pushed through the auto-updates. But since none seemed to be forthcoming, I downloaded kernel-2.6.25.10-86.fc9.i686 from Koji (http://koji.fedoraproject.org/koji/buildinfo?buildID=55121) and installed it without any problems using yum.
sudo yum --nogpgcheck localinstall kernel-2.6.25.10-86.fc9.i686.rpm kernel-devel-2.6.25.10-86.fc9.i686.rpm kernel-headers-2.6.25.10-86.fc9.i386.rpm
The new kernel fixes the WPA issue and my wireless network is back online again. If you are experiencing the same problem, I recommend the latest kernel build, which is working perfectly for me at the moment.
At this point, I decided to wait a couple of days for an updated kernel to be pushed through the auto-updates. But since none seemed to be forthcoming, I downloaded kernel-2.6.25.10-86.fc9.i686 from Koji (http://koji.fedoraproject.org/koji/buildinfo?buildID=55121) and installed it without any problems using yum.
sudo yum --nogpgcheck localinstall kernel-2.6.25.10-86.fc9.i686.rpm kernel-devel-2.6.25.10-86.fc9.i686.rpm kernel-headers-2.6.25.10-86.fc9.i386.rpm
The new kernel fixes the WPA issue and my wireless network is back online again. If you are experiencing the same problem, I recommend the latest kernel build, which is working perfectly for me at the moment.
Subscribe to:
Posts (Atom)
